What Hackers Actually Want From You: Tips to Protect Your Data
When people hear the word “hacker,” they picture hoodies, glowing screens, and someone targeting billion-dollar companies. That image is fun, but it misses the point. Most attacks are boring, fast, and aimed at regular people scrolling on the couch. You are not special, but your data is useful.
Hackers play a numbers game. They cast wide nets and wait for small mistakes. One weak password or careless click can be enough. Understanding their real goals makes protection feel less overwhelming and more practical.
They Want Easy Access, Not Drama
Hackers rarely chase complex targets unless there is a big payoff. They prefer unlocked doors. Reused passwords, outdated apps, and ignored updates create those doors. Convenience is often the enemy here. Once access is gained, the attacker moves quietly.
No flashing warnings. No movie-style chaos. They slip in, grab what they can, and move on. Silence keeps them profitable. This is why basic hygiene matters. Simple defenses block most casual attempts without effort or stress.
Your Accounts Are More Valuable Than You Think

Email accounts are gold. They unlock password resets, private conversations, and verification codes. With email access, attackers can fan out across your digital life. Social accounts come next, especially ones tied to shopping or ads.
Even accounts that seem boring can be traded or reused. Hackers bundle logins and sell them in bulk. One person’s leftovers become someone else’s shortcut. The goal is leverage. One login leads to another. The chain keeps growing until it breaks.
Personal Data Is the Long Game
Names, addresses, and phone numbers may feel harmless alone. Together, they paint a clear picture. That picture fuels scams, impersonation, and targeted messages that feel unsettlingly accurate. This is why scam texts sometimes sound personal.
They borrow details collected over time. Familiar language lowers defenses faster than threats ever could. Data ages well for attackers. Old information still works. That patience makes these operations effective. Over time, even small scraps of information can be stitched together into profiles that feel uncomfortably precise.
They Rely on Habit and Distraction

Hackers understand human behavior better than code. People skim messages. They click quickly. They trust familiar logos and urgent language. That is the real opening. Phishing emails work because they blend in. Fake alerts look like real notifications. The goal is not brilliance. It is believability. A moment of pause changes everything. Reading twice beats reacting once. That small habit shuts down many attacks instantly. Busy moments, tired eyes, and multitasking brains are exactly the conditions attackers count on to slip past unnoticed.
Protection Is About Friction, Not Fear
You do not need to become paranoid or technical. You just need to be slightly harder to target than the next person. Hackers avoid friction. Extra steps push them elsewhere. Using different passwords slows them down. Updates close old gaps. Logging out cuts lingering access. None of this is exciting, but it works.
Think of security like locking your bike. You are not stopping every thief. You are stopping …









 One of the most prevalent myths is that virtual receptionists need more personal touch of in-house receptionists and come across as impersonal and robotic. This misconception stems from believing that virtual receptionists are merely automated systems or AI-driven bots. In reality, virtual receptionists are often real people who are trained to handle calls professionally and courteously. They can offer personalized interactions by accessing customer information and tailoring their responses to meet individual needs.
One of the most prevalent myths is that virtual receptionists need more personal touch of in-house receptionists and come across as impersonal and robotic. This misconception stems from believing that virtual receptionists are merely automated systems or AI-driven bots. In reality, virtual receptionists are often real people who are trained to handle calls professionally and courteously. They can offer personalized interactions by accessing customer information and tailoring their responses to meet individual needs.
 There is a misconception that virtual receptionists are limited to basic tasks like answering calls and taking messages. In reality, virtual receptionists can handle a wide range of
There is a misconception that virtual receptionists are limited to basic tasks like answering calls and taking messages. In reality, virtual receptionists can handle a wide range of 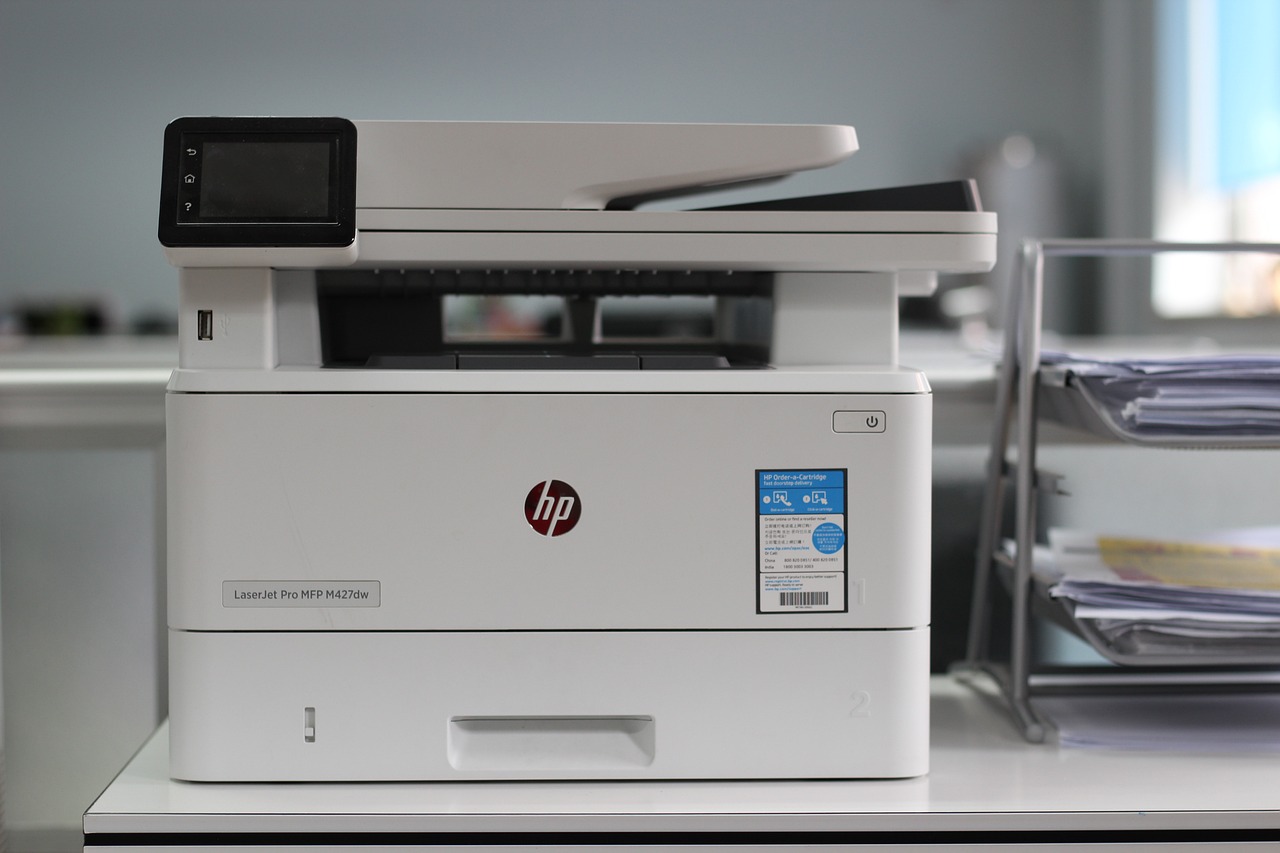
 In the age of connectivity, wireless capabilities have become a staple in modern printers. Wi-Fi connectivity allows users to print documents and photos directly from their smartphones, tablets, or computers without the need for cumbersome cables. This feature not only enhances convenience but also promotes a clutter-free workspace.
In the age of connectivity, wireless capabilities have become a staple in modern printers. Wi-Fi connectivity allows users to print documents and photos directly from their smartphones, tablets, or computers without the need for cumbersome cables. This feature not only enhances convenience but also promotes a clutter-free workspace.




 If you have kids, it’s important to set parental controls on their Android devices. With a spy app, you can keep track of what they’re doing online and make sure they’re not accessing inappropriate content.
If you have kids, it’s important to set parental controls on their Android devices. With a spy app, you can keep track of what they’re doing online and make sure they’re not accessing inappropriate content. It’s important to create data backups of your Android device. If something happens to your phone, you’ll lose all your data if you don’t have a backup.
It’s important to create data backups of your Android device. If something happens to your phone, you’ll lose all your data if you don’t have a backup.
 In digital communication systems, the user identities take the form of entries and attributes in the database. The idea is to gather the attributes to provide an improved user experience and better service. Your identity is defined when you sign up for the system. When registering, some attributes are gathered, such as social security, phone number, and email address. You should note that the registration process varies from one system to another.
In digital communication systems, the user identities take the form of entries and attributes in the database. The idea is to gather the attributes to provide an improved user experience and better service. Your identity is defined when you sign up for the system. When registering, some attributes are gathered, such as social security, phone number, and email address. You should note that the registration process varies from one system to another. It is challenging to remember several passwords and usernames to access your banks, websites, and social networks. This becomes challenging for many people. With identity management solutions, people can get an identity that offers access to various systems. For instance, single sign-on (SSO) systems allow partners and customers to access various external and internal applications. In this way, user experience is not compromised.
It is challenging to remember several passwords and usernames to access your banks, websites, and social networks. This becomes challenging for many people. With identity management solutions, people can get an identity that offers access to various systems. For instance, single sign-on (SSO) systems allow partners and customers to access various external and internal applications. In this way, user experience is not compromised.
 The truth is that technology solutions are not one-size-fits-all. Thus, your IT support partner ought to understand this and provide custom services that suit your business needs. It is advisable to start with shorter contracts that evaluate working relationships that support packages. The right company should provide you with recommendations that can save you money while getting the services you need.
The truth is that technology solutions are not one-size-fits-all. Thus, your IT support partner ought to understand this and provide custom services that suit your business needs. It is advisable to start with shorter contracts that evaluate working relationships that support packages. The right company should provide you with recommendations that can save you money while getting the services you need.


 The church is among the oldest institutions. It has been there for a long, from even before digital technology came about. The operations of churches, however, have changed quite a lot over the recent years, thanks to digital technology. The impact is seen on communication, worship, and administration, among many other elements. Some of the ways digital technology affects church operations are highlighted below.
The church is among the oldest institutions. It has been there for a long, from even before digital technology came about. The operations of churches, however, have changed quite a lot over the recent years, thanks to digital technology. The impact is seen on communication, worship, and administration, among many other elements. Some of the ways digital technology affects church operations are highlighted below. Church Services
Church Services
 Before entrusting your data to a cloud backup system, you need to ensure that your data is safe. In this case, durability refers to the system’s ability in the backup process. For example, they might claim that only one out of a million files is lost. It is a good idea to determine the threshold and talk to them about whether they can achieve it or not.
Before entrusting your data to a cloud backup system, you need to ensure that your data is safe. In this case, durability refers to the system’s ability in the backup process. For example, they might claim that only one out of a million files is lost. It is a good idea to determine the threshold and talk to them about whether they can achieve it or not.